Cloud computing technology provides organizations with a shared pool of computing resources over the internet, with low costs and guaranteed availability.
While using cloud technology offers many advantages compared to on-prem models (scalability, control, cost reduction etc.), it’s important to realize that cloud environments are vulnerable to both inside and outside attacks.
How One AI-Driven Media Platform Cut EBS Costs for AWS ASGs by 48%

To protect the cloud from cyber-attacks organizations, have to take some precautions and make sure to use latest cybersecurity solutions.
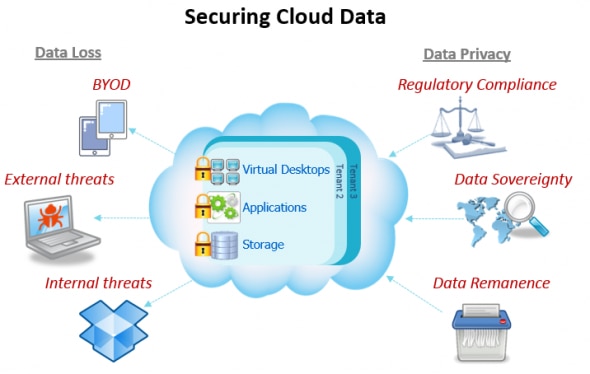
The issues regarding cloud security are somewhat complex, but they fall into two broad categories:
- Security issues faced by cloud providers (organizations providing software-, platform-, or infrastructure-as-a-service via the cloud)
- Security issues faced by their customers (companies or organizations who host applications or store data on the cloud)
Cloud security incidents often stem from a poor understanding of the shared responsibility model, which governs how cloud users and providers both shoulder the burden of security.
In this article, we’ll take a look at the most common cloud attack vectors, and what you can do to protect your business against cyber threats.

Cloud attack vectors
An attack vector is a path or means by which a hacker can gain access to a computer or network server in order to deliver malicious outcome. Attack vectors enable hackers to exploit system vulnerabilities, including the human element.
Attack vectors include viruses, e-mail attachments, Web pages, pop-up windows, instant messages, chat rooms, and deception. All of these methods involve programming (or, in a few cases, hardware), except deception, in which a human operator is fooled into removing or weakening system defenses.
Denial of Service (DoS)/Distributed Denial of Service (DDoS) attacks
A DoS/DDoS attack renders a website unavailable to users, but a successful one will hit an entire online user database. In a DoS attack, a perpetrator can use a single Internet connection to exploit a software vulnerability or flood the target with fake requests and finally cause that the site is made unavailable and prevent it from responding to requests from the legitimate users.
Or, the attack can be launched from multiple connected devices that are distributed across the internet, in an orchestrated Distributed Denial of Service attack, or DDoS.
The first step in launching a Distributed Denial of Service (DDoS) attack is to recruit an army of bots. In order to turn a computer into a bot, attackers develop specialised malware which they spread to as many vulnerable computers as possible. Malware can spread via compromised websites, e-mail attachments, or through an organisation’s network. Any users tricked into running such malware will unintentionally turn their computer into a bot, and provide attackers with an access point to their computer.
Once a computer turns into a bot, it connects to the attacker’s control circuits and it begins to accept orders from these centralised machines. The orders from the commanding control servers include directions for launching an attack from bots malware to a particular target using selected attack methods.
An army of bots is named a botnet and it usually consists of thousands of bots. Any time the botnet owners want to launch an attack, they send messages to their botnet’s control servers. Any affected machine in the botnet will comply by launching a coordinated, well timed distributed attack known as the Distributed Denial of Service.
The usual targets for DoS or DDoS attacks typically include websites hosted on high-profile web servers (such as credit card payment gateways, banks, government bodies) and most commonly, the target machine is so overwhelmed with external communication requests that it can either respond too slow, or not at all, and is considered effectively – unavailable.
The cloud model gives the DoS attack even more computational power. This problem is further aggravated when DDoS comes into picture as more machines will be compromised to attack large number of systems. We’ve written about DDoS attacks before, so take a look if you want to learn more about this specific type of cyber-attack.
Cloud malware injection attacks
Malware injection attacks are done to take control of a user’s information in the cloud. For this purpose, hackers add an infected service implementation module to a SaaS or PaaS solution or a virtual machine instance to an IaaS solution. If the cloud system is successfully deceived, it will redirect the cloud user’s requests to the hacker’s module or instance, initiating the execution of malicious code. Then the attacker can begin their malicious activity such as manipulating or stealing data or eavesdropping.
The most common forms of malware injection attacks are cross-site scripting attacks and SQL injection attacks. During a cross-site scripting attack, hackers add malicious scripts (Flash, JavaScript, etc.) to a vulnerable web page.
Cross-cloud attacks
It’s common for cyberattackers to use public cloud environments to infiltrate on-prem data centers.
These types of threats occur when customers move one of their workloads into a public cloud environment, such as Amazon Web Services or Microsoft Azure, and use Direct Connect (or any other VPN tunnel) to move between the public cloud into the private cloud. An attacker who breaches one of the environments can then move laterally, under the radar of security tools.
After the attacker scans the environment, he can use traditional vulnerabilities and exploits to gain an advantage in the public cloud.
The threat could be caught in the public cloud, he continues, but defenses are weaker there than they are in on-prem environments. An attacker has an advantage in moving between public and private clouds, and can use his position to persist in a target network.
Side channel attack
This attack is directed to compromise IaaS by placing a virtual machine co-resident to the victim’s virtual machine. This attacks targets cryptographic implementation in system.
The attack is done in two phases:
- Placing malicious virtual machine next to the target VM
- Extracting useful information from target virtual machine
Insider attacks
Insider attacks remain one of the top threats for various organizations, even if you don’t use cloud infrastructure. While most employees are trustworthy, it’s always a good idea to have a clear understanding of who has access to certain files and documents. Every organization should have multi-layered security policies in place, meaning that employees should have access only to those documents that are directly related to their everyday work.
It’s actually easy to implement such policies, but people often overlook them.
Cloud attack counter measures
We’ve discussed some of the most common cloud computing attack vectors malicious actors use to achieve their goals.
So, the next question is – how can organizations protect themselves from such attacks?
Encrypt data
To keep data secure, the front line of defense for any cloud system is encryption. Encryption methods utilize complex algorithms to conceal cloud-protected information.
To decipher encrypted files, would-be hackers would need the encryption key. Although encrypted information is not 100% uncrackable, decryption requires a huge amount of computer processing power, forensic software, and a lot of time.
Data in the cloud environment needs to be encrypted at all stages of its transfer and storage:
- at the source (on the user’s side)
- in transit (during its transfer from the user to the cloud server)
- at rest (when stored in the cloud database)
Use strong passwords and multi factor authentification
Instead of simple username and password authentication check, multifactor authentication must be implemented.
There are various tools that require both static passwords and dynamic passwords. The latter confirms a user’s credentials by providing a one-time password on a mobile phone or using biometric schemes or hardware tokens.
Trust, but verify
You have to validate the faith you put in your cloud provider. Trust is essential because everyone must have access to your infrastructure if you are going to move and build quickly. But it’s essential that you also monitor and audit continuously so you can verify business-critical activity and manage risk effectively.
Detect intrusions
Provide your cloud-based solution with a fully managed intrusion detection system that can detect and inform about the malicious use of cloud services by intruders. Use an intrusion detection system that provides network monitoring and notifies about the abnormal behavior of insiders.
Conclusion
While using cloud technology offers many advantages compared to on-prem models (scalability, control, cost reduction etc.), it’s important to realize that cloud environments are vulnerable to both inside and outside attacks.
Make sure you employ the counter measures we have mentioned to decrease the probability of a cyber-attack on your cloud infrastructure.
If you have any questions about how to effectively protect your cloud infrastructure, or how to optimize your cloud performance and reduce costs, contact us today to help you out with your performance and security needs.






