Sign up to our Newsletter
Phishing is a method employed by cyber-criminals to access email accounts and systems using deception rather than defeating security protections.
In basic phishing attacks, cyber-criminals send an email that appears to be legal, tempting the victim to open an attachment or click on a link. This click could result in loading malware onto the victim’s computer or it could take the victim to a realistic-looking website. In several cases, the aim is to capture user credentials without the knowledge of the victim.
How One AI-Driven Media Platform Cut EBS Costs for AWS ASGs by 48%

Cyber-criminals have discovered that it is usually easier to delude a victim into clicking a link instead of breaking through technology defenses.
Phishing attacks are becoming more advanced in their exploitation of social engineering techniques. In most cases, fraudsters try to frighten a recipient by providing a seemingly important reason that the recipient should divulge their personal data. Such messages usually contain threats to block an account if a recipient does not fulfill the requirements in them.

For instance, “if you do not provide your personal data by the end of the week, your account will be blocked”. Ironically, it is not unknown for phishers to make reference to the necessity of improving anti-phishing systems as one of the reasons for the disclosure of confidential information. A typical ruse might be “if you want to secure yourself against phishing, click the link and enter your user name and password”.
According to phishing.org, the first phishing lawsuit was filed in 2004 against a Californian teenager who created the imitation of the website “America Online”. With this fake website, he was able to gain sensitive information from users and access the credit card details to withdraw money from their accounts. Other than email and website phishing, there’s also ‘vishing’ (voice phishing), ‘smishing’ (SMS Phishing) and several other phishing techniques cyber-criminals are constantly coming up with.
From beginning to end, the process involves:
- Planning. Phishers decide which business to target and determine how to get e-mail addresses for the customers of that business. They often use the same mass-mailing and address collection techniques as spammers.
- Setup. Once they know which business to spoof and who their victims are, phishers create methods for delivering the message and collecting the data. Most often, this involves e-mail addresses and a Web page.
- Attack. This is the step people are most familiar with — the phisher sends a phony message that appears to be from a reputable source.
- Collection. Phishers record the information victims enter into Web pages or popup windows.
- Identity Theft and Fraud. The phishers use the information they’ve gathered to make illegal purchases or otherwise commit fraud. As many as a fourth of the victims never fully recover
Common phishing attacks
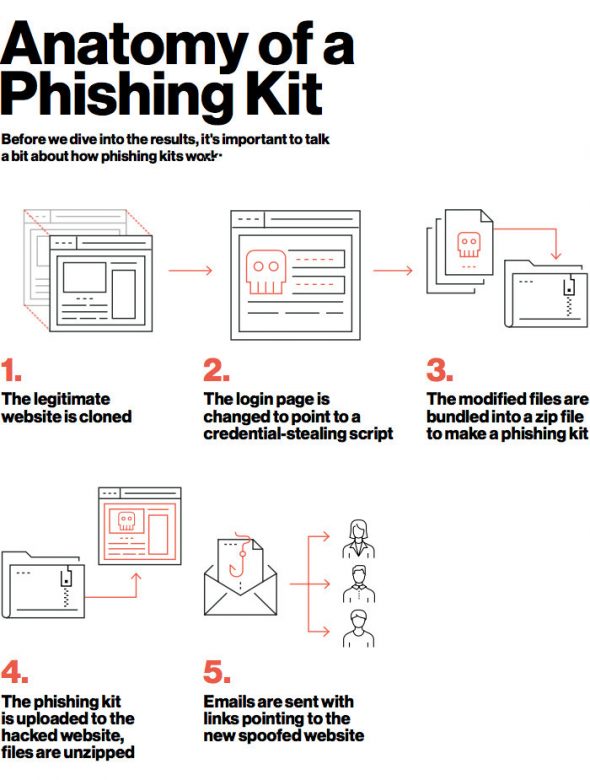
The availability of phishing kits makes it easy for cyber criminals, even those with minimal technical skills, to launch phishing campaigns. A phishing kit bundles phishing website resources and tools that need only be installed on a server. Once installed, all the attacker needs to do is send out emails to potential victims. Phishing kits as well as mailing lists are available on the dark web. A couple of sites, Phishtank and OpenPhish, keep crowd-sourced lists of known phishing kits.
The Duo Labs report, Phish in a Barrel, includes an analysis of phishing kit reuse. Of the 3,200 phishing kits that Duo discovered, 900 (27 percent) were found on more than one host. That number might actually be higher, however.
Email phishing
A phishing email is a fake email that appears to be like a crucial communication sent by a popular website or a bank. This email puts forth a tone of urgency and thus succeeds in tricking you into downloading an attachment or clicking on a link.
You will be taken to a fake website when you click on a link in a phishing email. This website could just drop a virus on your device or it could ask you to share classified information.
In many cases, downloading an attachment will infect your computer with a virus.
Phishing by SMS
This phishing attack that uses SMS is known as SmiShing. You will get an SMS, for instance, a WhatsApp message, informing you about an incredible offer. In this SMS you will be asked to redeem the offer by clicking on a link. After you click this link, you will be taken to a fake website that could infect your device with a virus or ask you to share confidential information.
Phishing by call
In a phishing call scam, you will get a phone call from a person acting like a bank manager, a software firm employee, or a known organization. This phishing call aims at tricking you into sharing private and vital details such as ATM PIN, expiry date, CVV, debit card number, and OTP.
Spear phishing
Spear phishing attacks a specific person or organization, often with content that is tailor made for the victim or victims. It requires pre-attack reconnaissance to uncover names, job titles, email addresses, and the like. The hackers scour the Internet to match up this information with other researched knowledge about the target’s colleagues, along with the names and professional relationships of key employees in their organizations. With this, the phisher crafts a believable email.
How to prevent phishing attacks
Protect your personal information
To prevent yourself from becoming a victim of a phishing scam, you will have to be extremely cautious with your personal information including your passwords and usernames.
When you enter your password/username and several other information, that information gets transmitted to the con artist, who can actually misuses it at a later stage. A few phishing scams divert you to a deceitful website that looks like your bank’s website or a similar trusted source.
Look out for suspicious emails and links
Do not click links sent along with suspicious emails. Addresses that appear to be official, could usually comprise of conspicuous differences that redirect you to a fraudulent site.
Be extremely suspicious of any emails sent to you from trustworthy entities like your bank. Also, avoid clicking on the link and instead type in the web address of the institution into the browser in order to access the website. Banks and financial organizations use monitoring systems to prevent phishing. Individuals can report phishing to industry groups where legal actions can be taken against these fraudulent websites.
Verify site’s security
It’s natural to be a wary about supplying sensitive financial information online. As long as you are on a secure website, however, you shouldn’t run into any trouble. Before submitting any information, make sure the site’s URL begins with “https” and there should be a closed lock icon near the address bar. Check for the site’s security certificate as well. If you get a message stating a certain website may contain malicious files, do not open the website.
Conclusion
Phishing is one of the most common cyber-attacks. Since it mostly relies on exploiting the human factor, even the most robust cyber-security techniques can fail to prevent such attacks, despite the advanced filters these systems employ. There’s no universal solution to deal with phishing attacks, but aside from protecting your personal information and being cautious about suspicious emails, you can always consult specialists to help protect your enterprise.
If you have any questions about how we can help you protect your website and business from cyber-attacks, contact us today to help you out with your performance and security needs.






