Hosting, Hardware & Networking
Making IT happen, anywhere.
Local boots on the ground is key for quick, cost-effective business expansion. Our international network of technical teams, data centers, and logistic centers, makes it all a breeze – from an offshore office or server to equipping your newest recruit for remote work. We plan, execute, and hand you the key to state-of-the-art infrastructure, optimized for your every demand.

Go Beyond Legacy Solutions
We at GlobalDots hunt for the most cutting edge and relevant technologies out there.
Once tested and found qualified we bring you the most certified innovative products out there for every pressing use case.
Our Hosting, Hardware & Networking Partners
-
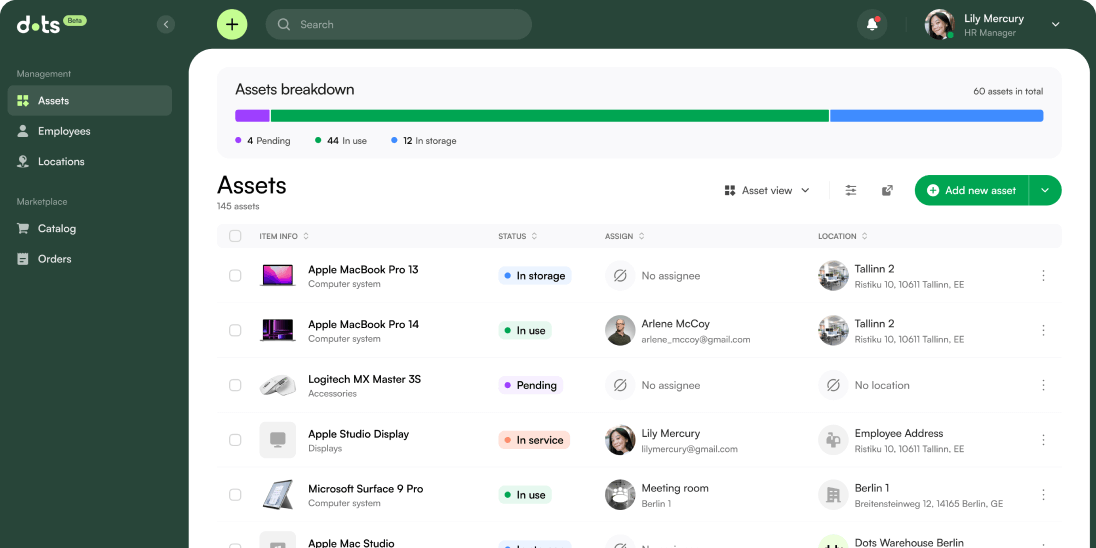
Dots
A powerful ITAM software, combined with a world-class logistics network
-
Corporate IT
Servers for on-premise data storage and networking, plus all endpoint devices and peripherals – both for offices and remote teams.
-
Colocation & Hosting
The full range of data storage & networking services: dedicated & managed web hosting, managed physical & virtual data centers, including support, migration, and managed services.
-
Internet & Connectivity
A complete internet connection & security solution to support enterprise networking worldwide.
-
Hardware (Procurement as a Service)
Taking the load of negotiation, benchmarking and purchase off your teams while leveraging our powerful commercial position.
-
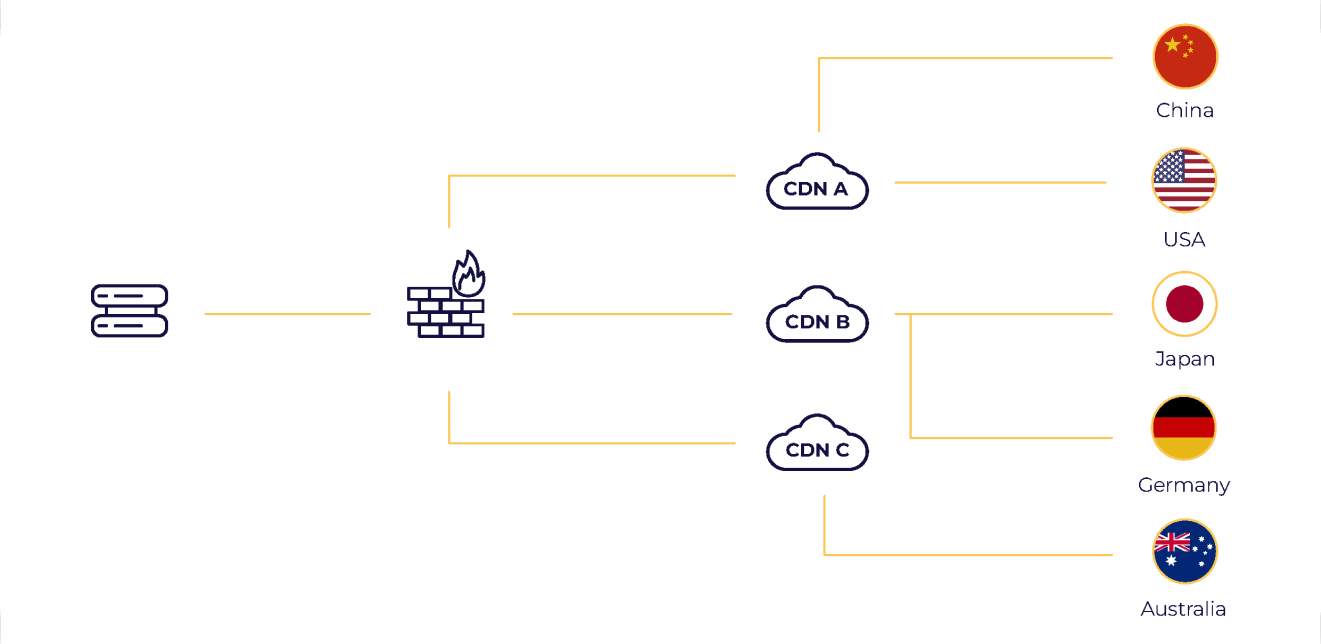
China Connectivity
One contact for the full suite of Mainland China colocation, networking, connectivity, and security, all by licensed providers.
-
Network Operations Center (NOC)
Flexible, modular network service solution delivered by experts, 24/7/365
-
SD-WAN and SASE
Experience enterprise networking as a cloud-based service, dramatically reducing complexity and TCO.
What makes a global-scale IT partner
As you shut offices down and grow your remote teams, one partner handling both processes simultaneously, on both technical and logistical aspects, is priceless.

Strategizing your data storage according to your business needs & plans, choosing the right hardware, then customizing and configuring it, gets the full load off your shoulders.

Tap into the Cloud’s agility and speed benefits by choosing a partner capable of supporting hybrid infrastructures or full cloud migration and managed services.

To quickly and cost-effectively execute global expansion, seek a partner with local connections on your geos of interest: to vendors, technical teams, and logistics service providers.

Stay Cloud-to-Date
The world of cloud changes quickly. Stay up-to-date with the latest trends & innovation, extensively explored in our resource library.
-
Cloud SecurityWhy C-Suite Executives Are Switching from VPNs to ZTNA
Hybrid workforces and cloud-first strategies have exposed the cracks in VPNs. Designed for simpler times, these legacy tools now create more problems than they solve. They slow your team down, leave security gaps, and make scaling a headache. How do you secure remote access without these hurdles? The answer is Zero Trust Network Access (ZTNA). […]
-
Web SecurityWeak Defences: The Most Hackable Sports Passwords
We get it. Thinking of another password that you haven’t used before can be frustrating – especially when we have to change or update our passwords so regularly. But while it might be tempting to use your favourite sports teams and clubs as passwords, it’s a risky move for your cyber security. Using unique passwords […]
-
Web SecuritySolving Network Security Issues for Rapidly Growing Global Businesses
Introduction Ryohin Keikaku is a global manufacturing and retail company that handles everything from product planning to sales for products known as “Mujirushi-Ryohin” in Japan and “MUJI” overseas. To keep pace with its rapid expansion—adding 100 new stores annually in Japan—and its growing global presence, now spanning 225 locations across 20 countries, including 50 stores […]
-
Cloud SecurityRethinking IT Security to Build Resilience for the Modern Threat Landscape
The recent two decades have changed how applications are built, delivered, and used. We used to have isolated networks with predictable entry points, but today, that has been replaced with a dynamic, interconnected web of APIs. The consequence of this is the dissolution of the traditional security perimeter. Today, protecting a single network boundary doesn’t […]
-
Cloud SecurityClosing the Gaps in API Security: How to Build Visibility and Protection for Modern Enterprises
APIs may be your organization’s greatest enabler, but without proper context, they can become its Achilles’ heel. APIs power modern digital ecosystems, connecting applications, enabling seamless machine-to-machine communication, and driving operational efficiencies. However, as APIs become the backbone of enterprises, they also represent an expanding attack surface — one that traditional Web Application and API […]
-
Cloud Cost OptimizationWhat are the biggest business worries in 2025?
No matter their industry or profession, practically every business in the UK and around the world has concerns for the year ahead. Whether it’s employee retention, rising costs, or simply finding new customers, each and every business owner has to make crucial decisions around these fears in order to successfully lead their company forward. However, […]
-
Cloud SecurityFrom 2024 to 2025: The Evolving DDoS Threat Landscape
The numbers from the DDoS landscape tell a troubling story. In Q3 2024, DDoS attacks reached unprecedented levels, reaching a record-breaking Tbps and billion packet-per-second attack. These hyper-volumetric campaigns tested the resilience of global networks against attackers who are becoming faster, smarter, and more resourceful. They also became a wake-up call for IT leaders who […]
-
Cloud SecurityUniversal ZTNA: How Does it Compare to Traditional ZTNA?
How will you protect your network as cloud-first strategies and hybrid workforces redefine the modern business landscape? While Traditional Zero-Trust Network Access (ZTNA) solutions laid the foundation for secure access, Universal ZTNA is rewriting the rules. Imagine a solution that unifies your security policies across all environments, simplifies management, and scales easily. That’s Universal ZTNA. […]
-
Cloud Cost Optimization4 Common Kafka Installation Errors – And Proven Steps to Avoid Them
Apache Kafka is the platform of choice for real-time data processing, but getting it up and running can feel like an uphill battle. With high throughput and fault tolerance, companies like Spotify rely on this distributed streamlining platform to deliver seamless services for over 600 million global users – supporting everything from log aggregation and […]
-
Cloud SecurityHow eBPF Enhances Threat Detection and Cloud Observability
Cloud-native environments are growing more complex and distributed. This growth makes security and performance observability even more critical to modern DevSecOps strategies. Enter eBPF (Extended Berkeley Packet Filter), a revolutionary technology that can run sandboxed programs in a privileged context such as the operating system kernel, which enables enhanced: Its ability to extend kernel capabilities […]
-
Cloud Cost Optimization4 Proven Ways to Minimize Your AWS MSK Cost
The very tools designed to streamline cloud operations can sometimes stretch budgets thin. One good example is managing the costs associated with Amazon Managed Streaming for Apache Kafka (MSK). While AWS MSK simplifies deploying and scaling Kafka clusters, the costs can stack up if not optimized. Here’s how you can rethink your AWS MSK deployment […]
-
Cloud SecurityRotating Pen Test Vendors Isn’t the Best Approach: Here’s Why
How do organizations ensure their penetrating testing remains insightful and free from complacency? For many years, the answer was vendor rotation — the practice of changing pen test vendors every few years. But does this approach still make sense today? While it once served a crucial purpose, the administrative burden it creates can be significant. […]
-
Cloud SecurityThe Reconnaissance Playbook of a Kubernetes Attacker
As Kubernetes gained widespread adoption in production environments, it became more attractive to attackers. Its distributed and dynamic nature made it a favorite for scalable and flexible containerized applications, but it also introduced some vulnerabilities and misconfigurations that can be exploited. For an attacker looking to exploit a Kubernetes cluster, reconnaissance is a critical first […]